Introduction
What is software? A complete 2026 guide covering types of software, system architecture, SaaS, security, enterprise infrastructure, and digital strategy.
If hardware is the physical body of a machine, software is its intelligence, coordination system, and behavioral logic combined.
But in 2026, software is far more than programs running on laptops. It is the invisible operating layer of:
- Global financial markets
- E-commerce ecosystems
- Healthcare infrastructure
- Government defense systems
- Telecommunications networks
- Cloud computing platforms
- Artificial intelligence engines
Every time you send a message, transfer funds, load a webpage, or authenticate into a secure dashboard, software orchestrates a chain of operations across multiple systems and geographic regions.
Software is not optional infrastructure. It is economic infrastructure.
To understand software today means understanding:
- How digital systems scale
- How data flows across networks
- How security layers protect assets
- How enterprises select and govern platforms
- How cost modeling influences technology strategy
- How distributed systems handle tradeoffs
- This guide will move you from beginner-level clarity to enterprise-aware mastery.
Why Software Powers the Modern World
Software governs nearly every digital process on Earth.
Consider a simple example: purchasing a product online.
Behind a single click:
- Your device sends an encrypted HTTPS request
- DNS resolves a domain name
- A CDN routes static assets
- A load balancer distributes traffic
- Application servers execute business logic
- Databases validate inventory
- Payment gateways verify transactions
- Fraud detection systems score risk
- Logging systems record events
- Monitoring tools track performance
This happens in seconds
Software coordinates:
- CPU scheduling
- Memory allocation
- Storage indexing
- Network routing
- Authentication protocols
- Encryption standards
- Access control policies
Without software, modern commerce collapses.
Without software, global communication halts.
Without software, supply chains stall.
In short: modern civilization runs on code.
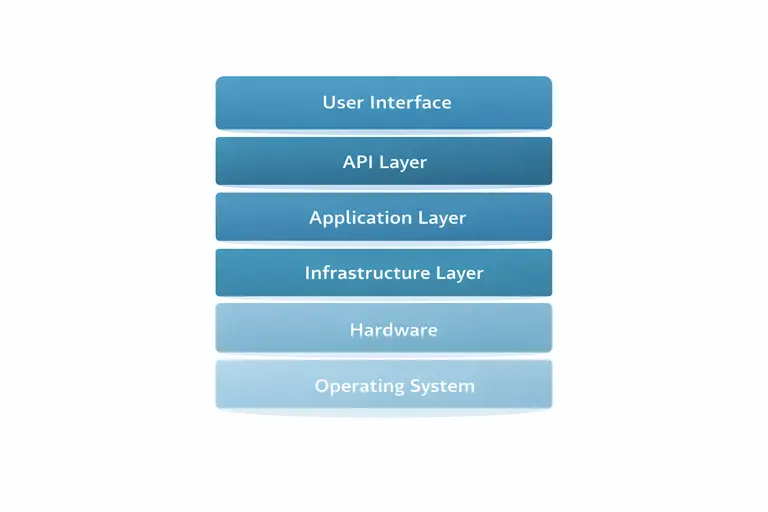
How Software Actually Works (Layered Technical Breakdown)
At a foundational level, software follows:
Input → Processing → Output
But real-world systems are layered across infrastructure, networking, application logic, and data storage.
Let’s examine a professional-grade architecture walkthrough.
👉 Read the guide: 10 Powerful Ways a Keyboard & Mouse Setup Can Transform Your Productivity
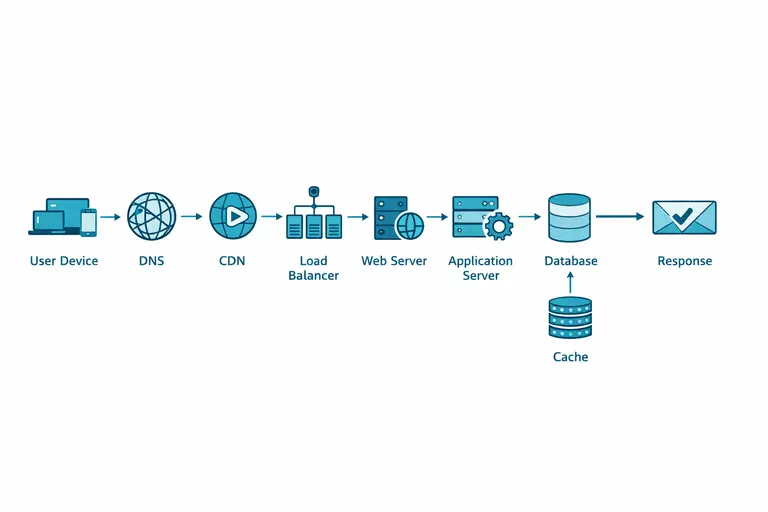
Real-World Request Flow Architecture
When a user visits a SaaS application, this chain often occurs:
- DNS Resolution
Domain is translated into IP address. - CDN Edge Routing
Static content delivered from geographically nearest node. - Web Application Firewall (WAF)
Traffic inspected for malicious patterns. - Load Balancer
Traffic distributed across multiple compute nodes. - Reverse Proxy
Routes requests to appropriate service. - Application Server
Executes business logic. - Microservice Call (if applicable)
Payment service, notification service, analytics service. - Database Cluster Query
Data retrieved or updated. - Cache Layer (Redis/Memcached)
Frequently accessed data served quickly. - Logging & Monitoring Systems
Metrics and traces recorded. - Response Returned to User
Target enterprise performance metrics:
- API response time under 200ms
- Database read under 10ms
- 99.99% availability or higher
- Mean time to recovery under 30 minutes
Understanding this architecture is foundational to enterprise software literacy.
Core Categories of Software
Software can be organized into major domains:
- System Software
- Application Software
- Developer & Programming Tools
- Cloud & SaaS Platforms
- Infrastructure & Hosting Software
- Networking & Security Systems
- Marketing & CRM Platforms
- Ecommerce Systems
- B2B Infrastructure Software
- DevOps & Administration Tools
Each category supports a different layer of digital operation.
System Software: The Invisible Engine
System software enables hardware functionality.
Operating Systems
Operating systems manage:
- Process scheduling
- Memory allocation
- Storage management
- Device drivers
- Security permissions
- Networking stacks
Without an operating system, no higher-level software can execute.
Enterprise environments often standardize OS deployment across servers for consistency and patch governance.
Device Drivers
Drivers enable hardware communication.
Examples:
- GPU drivers
- Network interface drivers
- RAID storage drivers
Outdated drivers can degrade performance or introduce security vulnerabilities.
Enterprise IT departments implement patch management schedules to mitigate risk.
Firmware
Firmware is embedded within hardware components.
Examples:
- Router firmware
- BIOS/UEFI
- Storage controller firmware
Firmware updates often resolve:
- Security vulnerabilities
- Performance bottlenecks
- Compatibility issues
Neglecting firmware updates increases long-term operational risk.
Application Software: Operational Productivity Layer
Application software is what end users directly interact with.
Categories include:
- Productivity suites
- Browsers
- Media software
- Communication platforms
- Security applications
- Financial software
Applications determine hardware requirements.
For example:
- Video production requires GPU acceleration and high RAM.
- Data science workloads require multi-core CPUs.
- Enterprise collaboration tools require strong network reliability.
Applications directly influence hardware investment decisions.
Developer & Programming Software
Programming tools create software.
Common categories:
- IDEs
- Version control systems
- Container orchestration tools
- Testing frameworks
- CI/CD pipelines
Enterprise developer environments often require:
- 32–64GB RAM
- Multi-core CPUs
- High-speed NVMe storage
- Virtualization capabilities
Developer tooling influences deployment speed and system reliability.
👉 Read the guide: Computer Hardware Basics Guide: Components, Performance, Reliability, Security & Lifecycle Management
Cloud Software & SaaS Explained
Cloud software runs on remote infrastructure.
Instead of installing locally, users access software through browsers or APIs.
This is Software as a Service (SaaS).
SaaS Benefits
- Automatic updates
- Elastic scaling
- Subscription pricing
- Global access
- Reduced hardware dependency
Most SaaS platforms use multi-tenant architecture to serve thousands of customers efficiently.
Cloud-native architecture dominates modern enterprise IT.
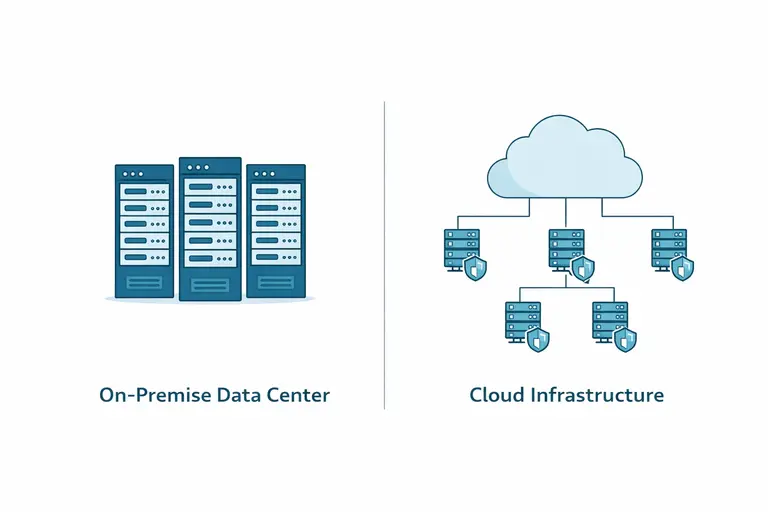
Web Hosting & Infrastructure Software
Web hosting provides the compute environment for applications.
Hosting models include:
- Shared hosting
- VPS
- Dedicated servers
- Cloud hosting
Enterprise hosting includes:
- Auto-scaling clusters
- Redundant availability zones
- Failover systems
- Continuous monitoring
- Infrastructure as Code deployment
Infrastructure software determines uptime and resilience.
Servers, Networking & Security Systems
Servers provide services to client devices.
They host:
- Websites
- Databases
- APIs
- Email systems
- Internal enterprise tools
Networking software governs:
- IP routing
- Firewall enforcement
- Subnet segmentation
- VPN tunnels
- Intrusion detection systems
👉 Read the guide: Enterprise IT Guide to Docks & Hubs: Architecture, Standards, Security, Performance & Deployment
Uptime Reliability Benchmarks
- 99.9% uptime = 8.7 hours downtime/year
- 99.99% uptime = 52 minutes/year
- 99.999% uptime ≈ 5 minutes/year
Higher reliability requires redundancy, monitoring, and proactive governance.
Microservices vs Monolithic Architecture
As software systems evolve from small applications into enterprise platforms serving thousands or millions of users, architecture becomes the most important long-term decision.
Two primary architectural models dominate modern software:
- Monolithic Architecture
- Microservices Architecture
Understanding both is essential for mastery.
Monolithic Architecture
A monolithic system is built as a single unified codebase. All business functions — authentication, billing, notifications, analytics, reporting — exist within one deployable unit.
Advantages:
- Simple initial development
- Easier debugging early on
- Lower infrastructure overhead
- Faster MVP launch
Disadvantages:
- Difficult to scale individual components
- Higher risk of cascading failure
- Slower deployment cycles at scale
- Harder to maintain as complexity grows
In early-stage startups, monolithic systems are often practical. But as systems scale, performance bottlenecks and deployment risk increase.
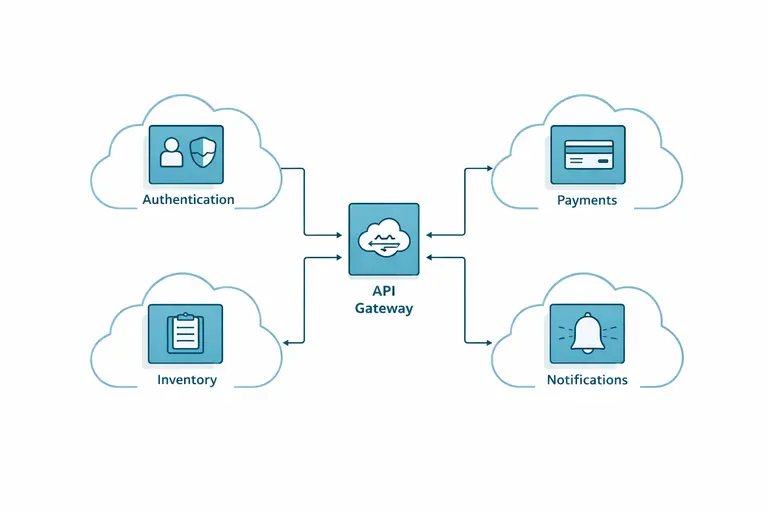
Microservices Architecture
Microservices divide applications into independent services, each handling a specific responsibility.
Examples in an e-commerce platform:
- Authentication service
- Product catalog service
- Payment service
- Inventory service
- Shipping service
- Notification service
Each service:
- Can scale independently
- Can be deployed independently
- Communicates via APIs
- Can use different technologies if needed
Advantages:
- Fault isolation
- Independent scaling
- Faster release cycles
- Improved team autonomy
Challenges:
- Increased infrastructure complexity
- Network latency considerations
- Requires orchestration tools (e.g., container schedulers)
- Higher observability requirements
Enterprise systems prefer microservices because they align better with growth and reliability objectives.
Distributed Systems Tradeoffs: The CAP Theorem (Expanded)
When software operates across multiple servers or regions, it becomes a distributed system.
Distributed systems must manage three guarantees:
- Consistency – All nodes see the same data simultaneously.
- Availability – Every request receives a response.
- Partition Tolerance – The system continues functioning despite network failures.
The CAP theorem states that in the presence of network partitioning, a distributed system can guarantee only two of the three properties.
In practical terms, partition tolerance is mandatory — networks fail. Therefore, systems must choose between:
- Consistency + Partition Tolerance
- Availability + Partition Tolerance
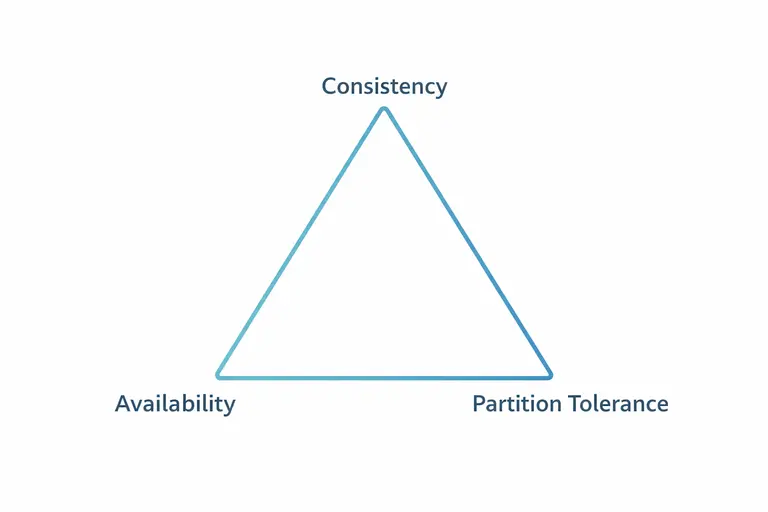
Business-Aligned Tradeoffs
Financial systems prioritize consistency. Accuracy outweighs short-term availability.
Content platforms prioritize availability. Minor data delays are acceptable.
Architectural mastery means aligning technical tradeoffs with business risk tolerance.
Event-Driven Architecture & Message Queues
Modern distributed systems often adopt event-driven architecture.
Instead of direct service-to-service calls, systems publish events.
Example:
- Order placed → Event published
- Payment service listens → Processes payment
- Inventory service listens → Updates stock
- Notification service listens → Sends confirmation email
This reduces coupling and improves resilience.
Message queue systems enable this pattern.
Benefits:
- Asynchronous processing
- Improved fault tolerance
- Load buffering during traffic spikes
Event-driven systems are critical in large-scale e-commerce and SaaS platforms.
API Rate Limiting & Traffic Governance
Public-facing APIs require traffic control.
Without limits:
- Malicious actors can overwhelm systems.
- Bugs can trigger cascading failures.
Rate limiting strategies include:
- Requests per minute limits
- Token bucket algorithms
- IP-based throttling
- User-tiered access controls
Enterprise systems combine rate limiting with monitoring and anomaly detection.
Database Indexing & Performance Modeling
Databases are often performance bottlenecks.
Indexing improves query speed by allowing the database to locate records without scanning entire tables.
Improper indexing leads to:
- Slow queries
- Increased CPU load
- Reduced scalability
Enterprise performance teams regularly audit:
- Query execution plans
- Index fragmentation
- Replication lag
- Read/write ratios
Database optimization can reduce latency dramatically — sometimes by over 70%.
Advanced Caching Deep Dive
Caching reduces database load and accelerates response times.
- Browser cache
- CDN cache
- Application memory cache
- Database query cache
Cache Layers
One of the hardest problems in computing is cache invalidation — ensuring users receive updated data.
Strategies include:
- Time-based expiration
- Event-triggered invalidation
- Write-through updates
Well-designed caching can reduce infrastructure cost while improving performance.
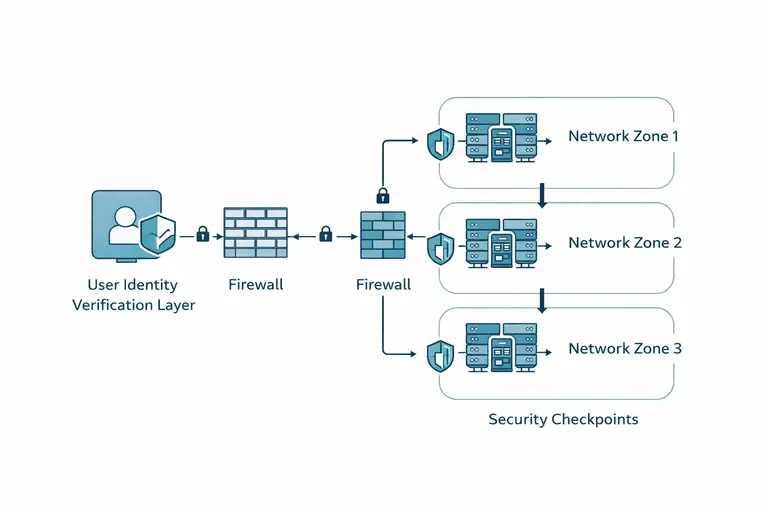
Zero Trust Security Architecture (Enterprise Modeling)
Traditional network security assumed internal networks were trustworthy.
Zero Trust eliminates this assumption.
Principles:
- Verify identity at every request
- Enforce least-privilege access
- Monitor continuously
- Segment networks
Zero Trust reduces lateral movement during breaches.
NIST Cybersecurity Framework Integration
The NIST Cybersecurity Framework (CSF) organizes security into:
- Govern
- Identify
- Protect
- Detect
- Respond
- Recover
This structured model helps organizations align technical controls with governance strategy.
Reference:
Link
Enterprise-grade software architecture should map security controls to these categories.
Encryption Strategy: Defense in Depth
Security requires layered encryption:
- TLS for in-transit encryption
- AES-256 for data at rest
- Key management systems (KMS)
- Hardware security modules (HSMs)
Encryption without key governance is incomplete.
Professional environments enforce strict key rotation policies.
👉 Read the guide: The Ultimate Guide to Productivity Gadgets for Home & Office 2026
Quantified Breach Case Study
IBM’s 2024 Cost of a Data Breach Report estimates the average global breach cost at $4.88 million.
Costs include:
- Incident response teams
- Regulatory fines
- Customer notification
- Lost business
- Reputation damage
Sophos research reports ransomware recovery costs exceeding $2 million in many cases.
Security budgets should be evaluated against potential breach cost exposure.
Observability, Reliability Engineering & Error Budgets
Enterprise software must be observable.
Observability tools capture:
- Logs (what happened)
- Metrics (how often)
- Traces (where delays occurred)
Reliability Metrics
- SLA – Customer promise
- SLO – Internal reliability goal
- SLI – Measured metric

Error Budgets (Operational Discipline)
If uptime target is 99.9%, allowable downtime is ~8.7 hours annually.
Error budgets allow organizations to balance:
- Feature velocity
- System stability
If error budgets are exhausted, releases pause until reliability improves.
This approach prevents reckless deployment.
Cost Modeling & FinOps (Enterprise Finance Layer)
Software cost modeling includes:
Direct Costs
- Licensing
- Infrastructure
- Subscription fees
- Implementation
Indirect Costs
- Downtime
- Security incidents
- Vendor lock-in
- Staff training
Cloud waste can account for 20–30% of infrastructure budgets.
FinOps practices:
- Usage monitoring
- Reserved instance planning
- Auto-scaling optimization
- Cost anomaly detection
Financial governance is essential in software strategy.
B2B Infrastructure Software: The Enterprise Backbone
While consumer software focuses on usability and convenience, B2B (business-to-business) infrastructure software prioritizes stability, scalability, compliance, and integration.
B2B infrastructure software includes:
- ERP (Enterprise Resource Planning) systems
- CRM platforms
- HR management systems
- Supply chain software
- Financial accounting systems
- Identity & Access Management (IAM) platforms
- Data warehousing systems
- Business intelligence dashboards
These platforms are deeply integrated into operational workflows.
ERP Systems
ERP software integrates:
- Finance
- Procurement
- Inventory
- Manufacturing
- Payroll
ERP software centralizes operational data, enabling cross-departmental coordination.
Failure in ERP systems can halt enterprise operations.
CRM Systems
Customer Relationship Management (CRM) platforms store:
- Contact records
- Sales pipelines
- Marketing interactions
- Customer service history
CRM platforms integrate with marketing automation tools to support revenue growth.
Identity & Access Management (IAM)
IAM systems manage:
- User authentication
- Multi-factor authentication (MFA)
- Role-based access control (RBAC)
- Single sign-on (SSO)
IAM is central to Zero Trust implementation.
DevOps & Administration Tools
DevOps combines development and operations to accelerate deployment while maintaining reliability.
Key DevOps tools include:
- CI/CD pipelines
- Container orchestration systems
- Infrastructure as Code (IaC) tools
- Monitoring platforms
- Configuration management systems
Continuous Integration / Continuous Deployment (CI/CD)
CI/CD automates:
- Code testing
- Security scanning
- Deployment to staging
- Production rollout
This reduces human error and accelerates release cycles.
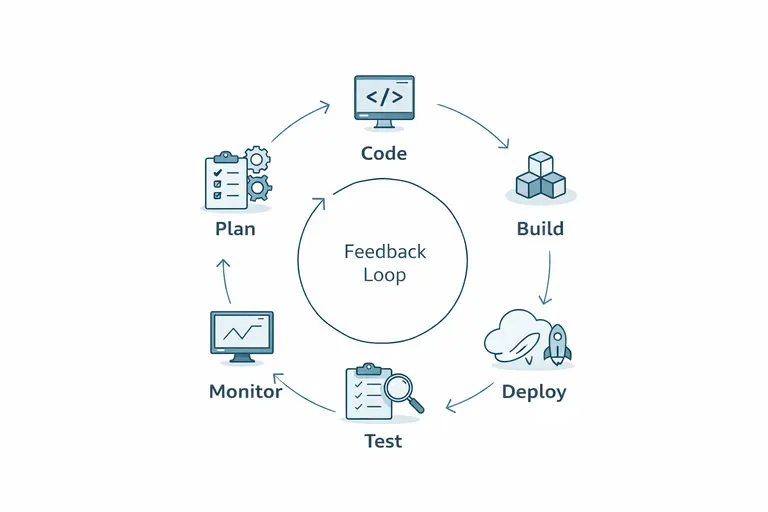
Infrastructure as Code (IaC)
IaC allows infrastructure to be defined through code.
Benefits:
- Reproducibility
- Version control
- Automated deployment
- Reduced configuration drift
Modern cloud environments rely heavily on IaC principles.
Administrative Tooling
Enterprise environments require:
- Patch management systems
- Endpoint monitoring
- Centralized logging
- Compliance auditing tools
- Backup orchestration platforms
Administrative tooling reduces operational risk.
Marketing Software & Automation Systems
Modern marketing is software-driven.
Marketing platforms automate:
- Email campaigns
- Lead nurturing
- Behavioral segmentation
- Conversion tracking
- Social scheduling
Automation example:
Visitor downloads whitepaper → Trigger email workflow → CRM updates lead score → Sales notified.
Marketing software integrates directly with CRM systems.
Marketing software directly impacts customer acquisition cost (CAC) and lifetime value (LTV).
E-commerce Enterprise Scaling Model
E-commerce infrastructure must scale dynamically.
Traffic Growth Stages
Stage 1 – Startup
- Single web server
- Shared database
- Manual backups
Stage 2 – Growth
- Load balancing
- CDN integration
- Automated backups
- Basic monitoring
Stage 3 – Enterprise
- Multi-region cloud deployment
- Auto-scaling clusters
- Read replicas
- Distributed caching
- Fraud detection AI
- Real-time monitoring
- Dedicated DevOps team
Downtime during peak traffic can result in significant revenue loss.
A one-hour outage during high-volume sales can cost millions for large retailers.
VPN Architecture & Secure Networking
VPN software establishes encrypted tunnels between endpoints.
Core VPN Components
- Encryption protocol
- Authentication mechanism
- Key exchange method
- Secure tunneling
Business VPN use cases:
- Remote workforce access
- Secure site-to-site connectivity
- Protection against packet sniffing
VPN performance considerations:
- Encryption overhead
- Server proximity
- Latency impact
VPNs are one component of layered cybersecurity.
Choosing the Right Software Stack (Strategic Framework)
Selecting software requires strategic evaluation.
Key questions:
- Does the software scale horizontally?
- Is the architecture cloud-native?
- Does it support API integrations?
- Is encryption enabled by default?
- Does it align with Zero Trust?
- What is total cost of ownership?
- What is vendor exit strategy?
- Does it support compliance standards?
- Is observability built-in?
- Can it handle 10x projected growth?
Software stack decisions influence:
- Infrastructure cost
- Security posture
- Operational agility
- Revenue scalability
Strategic software selection prevents expensive migrations later.
Governance, Compliance & Risk Modeling
Enterprise software decisions must consider regulatory compliance.
Common compliance frameworks:
- SOC 2
- ISO 27001
- GDPR
- HIPAA (for healthcare)
Governance involves:
- Risk assessment
- Vendor audits
- Data classification
- Access control enforcement
- Incident documentation
Failure to align with compliance requirements can result in fines and reputational damage.
The Future of Software in 2026 and Beyond
Software evolution is accelerating.
Key trends:
AI-Augmented Development
AI assists with:
- Code generation
- Testing automation
- Security vulnerability detection
- Predictive performance tuning
Serverless Computing
Serverless abstracts infrastructure management.
Benefits:
- Reduced operational overhead
- Automatic scaling
- Pay-per-execution pricing
Edge Computing
Processing closer to end users reduces latency.
Autonomous Monitoring
AI-driven observability tools predict failures before they occur.
Cybersecurity Evolution
Zero Trust becomes default architecture.
Software will become:
- More autonomous
- More adaptive
- More predictive
Organizations that master software infrastructure will outperform competitors.
Frequently Asked Questions
What is software in simple terms?
Software is a collection of digital instructions that tell hardware how to function.
What are the main categories of software?
System, application, cloud/SaaS, infrastructure, security, and enterprise software.
What is SaaS?
Software delivered via cloud subscription rather than local installation.
What is web hosting?
Infrastructure that enables websites and applications to operate online.
What is a server?
A computer designed to provide services to other devices.
What is the CAP theorem?
A distributed systems principle describing tradeoffs between consistency, availability, and partition tolerance.
What is microservices architecture?
An architectural style dividing applications into independent services.
What is event-driven architecture?
A model where services communicate via published events.
What is Zero Trust?
A security model requiring continuous identity verification.
What is encryption at rest?
Protection of stored data using cryptographic algorithms.
What is encryption in transit?
Protection of data while being transmitted across networks.
What is an error budget?
Allowed downtime within a defined reliability objective.
What is observability?
The ability to monitor system health through logs, metrics, and traces.
What is FinOps?
Financial management discipline for cloud cost optimization.
What is vendor lock-in?
Dependency on one provider’s ecosystem.
What affects software performance most?
Architecture design, scaling strategy, and infrastructure optimization.
What is infrastructure as code?
Managing infrastructure through version-controlled code definitions.
Why are updates critical?
They patch vulnerabilities and improve performance.
What is B2B infrastructure software?
Enterprise systems that support organizational operations.
What is the future of software?
AI-driven, automated, scalable, secure digital ecosystems.
Final Thoughts: Understanding Digital Power
Software is not just code.
It is:
- Economic infrastructure
- Security defense
- Operational backbone
- Innovation catalyst
- Competitive advantage
From operating systems and cloud platforms to VPN encryption and enterprise governance, software defines the structure of modern civilization.
Understanding software at an architectural, financial, and operational level transforms you from a user into a strategist.
Those who understand software infrastructure shape the digital future.
